Hackers have been exploiting a critical vulnerability in Cisco’s Catalyst SD-WAN products since at least 2023, according to the company. The bug allows remote takeover of networking devices used by large enterprises and government agencies.
The vulnerability has a maximum severity score of 10.0 and affects products that connect private networks over long distances. Exploitation grants hackers the highest level of permissions and allows them to maintain persistent, hidden access to spy or steal data.
Cisco researchers traced evidence of the exploitation back to 2023. Some affected organizations are critical infrastructure, though the company did not provide specifics. “Critical infrastructure” can refer to power grids, water supply, and the transportation sector.
Several governments issued a joint alert warning of global attacks. The alert included the United States, United Kingdom, Australia, Canada, and New Zealand. The governments stated that threat actors are targeting organizations “globally.”
The U.S. cybersecurity agency CISA ordered all civilian federal agencies to patch their systems by the end of the day. CISA cited an imminent threat and an unacceptable risk to the federal government. The agency stated it was aware of ongoing exploitation, noting it is currently running at reduced capacity due to a partial government shutdown.
Neither Cisco nor the governments attributed the attacks to a specific threat group or nation-state. One cluster of activity is tracked under the name UAT-8616.
This incident follows a similar vulnerability Cisco warned about in December. That bug, also rated 10.0, was in the Async software that runs most of its products. The Async vulnerability was being actively used to hack into customer networks.
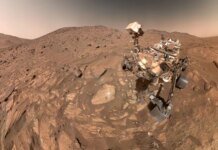
Featured image credit