How Software-Defined Vehicles are Redefining Architecture and Transforming Field Service Actions
Architectural Goal: Transition from a "Point-in-Time" hardware release to a "Continuous Evolution" software model.
Add bookmark  Preeti Sali
Preeti Sali
03/02/2026 
The automotive industry is currently navigating its most significant pivot since the assembly line: the transition from hardware-centric machines to Software-Defined Vehicles (SDVs).
In the traditional automotive world, a "Field Service Action" (FSA) was a heavy-handed logistical maneuver considered as a failure of hardware distribution. If a brake controller logic was flawed, the "fix" was a physical intervention often involving physical mailers, dealer appointments, and manual labor. Today, we are seeing an Architectural Decoupling where functional safety is managed as a distributed software system. As we pivot toward SDVs, the industry is moving toward isolating models where the vehicle’s functional safety is managed as a distributed software system, and the paradigm is shifting from grease and wrenches to automated validation and system wide evolution.
From a Systems Architecture perspective, by integrating security and automated verification into the heart of the development lifecycle, the goal is no longer just "building a car," but designing a resilient, updateable ecosystem that can resolve Field Service Actions (FSAs) via CI/CD pipelines rather than service bays and effectively ending the era of the physical recall.
The Architecture of the Shift: Centralized Compute
In an SDV, the architecture is centralized into high-performance computers (HPCs) using zonal gateways. This centralized "brain" allows us to treat vehicle software like a distributed cloud system. When a safety or compliance concern is raised, whether by internal telemetry or the National Highway Traffic Safety Administration (NHTSA), the response is no longer a partreplacement strategy, but a targeted software patch. This design pattern allows for:
- Abstraction of Hardware: Decoupling software from specific chips through a hardware abstraction layer (HAL).
- Service-Oriented Architecture (SOA): Moving from proprietary signals to standardized APIs (e.g., SOME/IP).
- Centralized Diagnostics: Real-time telemetry that identifies failures before they trigger a dashboard light.
- Hypervisors & Containerization: Running safety-critical RTOS (Real-Time Operating Systems) alongside infotainment Linux/Android on the same system on chip, ensuring that a "recall" patch for one domain doesn't crash the other.
- Delta Updates: Sending only the changed code blocks to minimize bandwidth and update time.
Designing for "Zero-Waste" Verification & Validation (V&V)
Managing 100+ software recalls across global regions for safety, emissions, and compliance requires more than just good code; it requires a robust Verification & Validation (V&V) ecosystem. The primary bottleneck in resolving is not writing the code- it’s the Validation Bottleneck. The modern FSA workflow mirrors a high-maturity design pipeline, the architecture must support Automated Validation to close the loop on NHTSA or regulatory concerns.
The biggest architectural hurdle in BEV field service is Data Silos. Historically, battery data, charging station handshakes, and drivetrain telemetry lived in disparate formats. Architecture isn't just about code; it’s about data flow. By standardizing segregated triage processes into a common data scheme, organizations can reduce "data seeking" time by over 50%.
Unified Triage Management (UTM)
By implementing Unified Triage Management, we normalize these data streams into a single Data Fabric. A unified data architecture allows for:
- Cross-Functional Traceability: Linking customer insights directly to a specific software build version and its validation history.
- Rapid Root Cause Analysis (RCA): Utilizing fleet-wide telemetry to identify if a failure is systemic or edge-case-specific. Architecturally, this is achieved by moving away from "Data Silos" to a Common Data Schema for vehicle telemetry.
- The Unified Solution: Implementing a centralized architecture where edge data from the fleet is normalized. This allows the system to correlate a battery thermal event with a specific software version and ambient temperature across the entire global fleet in minutes.
- Traceability Matrix: Every FSA (Field Service Action) should be bi-directionally linked. If the NHTSA raises a concern, the architect can trace that concern down to the specific line of code and the specific validation test that should have caught it.
The Automated Validation Loop
In the transition from manual processes to automated tools, the architecture must handle Dependency Mapping. To achieve an 80% improvement in operational efficiency, the V&V architecture must transition from manual bench testing to Hardware-in-the-Loop (HiL) and Software-in-the-Loop (SiL) automation.
A change in the motor control logic might affect the thermal cooling loop. Before a single bit is flipped over-the-air (OTA) we map human and system interactions. Drafting workflows with explicit dependencies and risks, we’ve moved from manual "check-box" compliance to automated tool-based, proactive enforcement where the validation code process approvals are baked into the PR (Pull Request). This architectural shift alone can improve operational efficiency by 80%, as the "recall" becomes a standard release train event rather than an emergency intervention. By drafting workflows that account for human-system interactions and dependencies, we create a "Shift-Left" environment where compliance is baked into the initial design.
The BEV "Safety Loop"
For safety-critical BEV systems, we implement a Triple-Check Architecture:
- On-Vehicle SIL/HIL Validation: Ensures the code runs safely on the target silicon.
- Cloud-Side Abstraction: Compares fleet-wide telemetry against expected performance models.
- Closed-Loop Feedback: Uses data analytics to monitor the success of the FSA patch in real-time and provides an immediate KPI on "Recall Closure Rate" without waiting for the dealer reports.
The Data Architecture: Solving the Telemetry Silo
A major hurdle in FSAs is the fragmentation of data. Creating a centralized data management architecture combines cost efficiency and performance of a data warehouse.
- The Data Lakehouse Model: Modern SDV architectures normalize edge data from the fleet. This allows organizations to store vast amount of raw data in a single repository and engineers to query vehicle health like a database.
- Shadow Mode Validation: Before deploying a fix, we run the new code in "Shadow Mode" on production vehicles. The code processes real-world data and makes decisions, but its outputs are silenced. This provides a massive-scale validation step without risking passenger safety.
Managing the Hybrid Fleet: The "Legacy-to-SDV" Transition Bridge
A major architectural challenge is that most OEMs aren't starting with a blank sheet. They are managing a "Hybrid Fleet" where some vehicles are fully software-defined and others are legacy. To truly decouple hardware from software, the architecture requires a sophisticated Middleware Layer. This is the "glue" that allows a software patch to be chip-agnostic.
- Cloud-Side Abstraction: For legacy vehicles, the "SDV" capabilities are often hosted in the cloud. We create a Cloud-Digital Twin that acts as a proxy for the legacy hardware, allowing us to use modern Triage and V&V processes even for vehicles with limited OTA capabilities.
- Adaptive AUTOSAR: Unlike Classic AUTOSAR (which is static, signal-based for deeply embedded, real-time safety systems with zero room for error e.g., airbags, braking), Adaptive AUTOSAR supports service-oriented communication designed for high performance computing e.g., ADAS, V2X. It allows us to deploy new "services" to the vehicle without reflashing the entire OS.
- ROS2: Excels as middleware communication, modularity and rapid prototyping with massive open source library making it a favorite amongst autonomous vehicle development.
- Container Orchestration at the Edge: We are seeing a move toward Kubernetes-like orchestration for vehicles. If a zonal controller is overloaded, the system can dynamically reallocate compute resources, a critical design pattern for maintaining functional safety during an OTA update.
Cloud-Side Abstraction and the BEV Data Fabric
In a modern SDV architecture, the "vehicle" does not end at the bumper. To manage complex Battery Electric Vehicle (BEV) ecosystems, architects must implement a Cloud-Side Abstraction layer. This layer serves as the digital connective tissue between the high-voltage hardware and the DevSecOps pipeline.
For a BEV, where battery health (State of Health – SOH) and thermal management are missioncritical, this abstraction is the primary defense against large-scale physical recalls.
The "Digital Twin" as an Architectural Proxy
When dealing with a fleet of 100+ software variants, it is impossible to physically validate every edge case on every vehicle trim. Instead, before a patch is ever pushed to a customer's vehicle, engineers we utilize Digital Twins, cloud-based virtual representations of the vehicle’s Electronic Control Units (ECUs). By running the fix on a virtual representation of the vehicle’s software stack, OEMs can simulate thousands of edge cases, different weather conditions, battery states, or sensor inputs, to ensure the patch doesn't introduce new regressions.
- Virtual BMS (Battery Management System): By mirroring the BMS in the cloud, we can run "What-If" scenarios. If telemetry suggests a specific cell-balancing logic is causing premature degradation in cold climates, we don't wait for a failure. We simulate a patch on the Digital Twin using real-world fleet data before pushing the fix.
- Shadow Mode Execution: This is the ultimate "Shift-Right" validation strategy. We deploy the new code to the vehicle's secondary partition. It runs in the background, consuming real sensor data (current, voltage, temperature), but its outputs are compared against the "live" legacy code in the cloud. If the cloud-side abstraction detects a divergence, the update is flagged before it ever takes control of the physical hardware.
In an SDV environment, a recall often isn't a failure of engineering; it's a scheduled deployment. The goal is to reach a state where the hardware is "future-proofed" enough that its capabilities evolve entirely through software iterations.
The Regulatory Architecture: Navigating UNECE R155 and R156
Architecture in the automotive world isn't just about performance; it’s about legal provenance. To resolve global software recalls, the system must be designed to comply with international standards like UNECE R155 (Cybersecurity) and R156 (Software Updates).
- Software Update Management Systems (SUMS): This is the architectural backbone that ensures every OTA update is tracked, authorized, and safe. It requires a cryptographic chain of custody from the developer’s IDE to the vehicle’s gateway.
- Compliance-as-Code: By integrating these regulatory requirements into the CI/CD pipeline, we transition from "checking for compliance" at the end of a cycle to "continuous compliance." This is where we see the 80% improvement in operations—moving the burden of proof from manual documentation to automated system logs, yielding massive operational gains.
Resilient Deployment: The OTA Update Pattern
The "End of the Physical Recall" depends on the reliability of the Over-the-Air (OTA) architecture. The real power of an SDV lies in the feedback loop. Of course, moving to a software-first model introduces risks; Safety-critical systems (steering, braking, powertrain) require SIL (Safety Integrity Level) certifications. In a legacy recall, an OEM might never know if a customer actually visited the dealer until months later. In the new model, we use critical data analytics and user testing to monitor the health of the fleet in real-time.
Designing for field resilience requires the below critical architectural patterns:
- A/B Partitioning: The "Golden Image" strategy. The vehicle maintains two separate memory partitions. The update installs on "Partition B" while the vehicle runs on "Partition A." If the update fails validation checks, the bootloader defaults back to A, preventing a "bricked" vehicle.
- Delta Compression: To manage global safety and compliance updates across millions of BEVs, the architecture must support delta patching – sending only the binary difference to reduce bandwidth and maximize success rates.
- End-to-End Security (SecOps): Integrating HSMs (Hardware Security Modules) to ensure that every update is cryptographically signed and verified before execution.
- End-to-End Encryption: Protecting the update pipeline from "Man-in-the-Middle" attacks that could compromise fleet safety.
- Zero-Trust Architecture: Ensuring that an update to the "infotainment" system cannot bridge into the "powertrain" domain via the gateway.
- Fleet Telemetry: Provides immediate KPIs on the success rate of a patch.
The Efficiency Dividend: From Reactive Recalls to Proactive Patches
Moving from a manual, reactive posture to an automated, proactive model isn't just a technical win; it’s an operational revolution. By standardizing segregated processes and automating workflows, organizations can see efficiency gains of up to 80% in their operations.
The "Physical Recall" is often a logistics nightmare. In 2023, the automotive industry saw approximately 33.6 million to 35 million vehicles recalled across the United States alone. This surge was driven by increasingly complex vehicle technologies, with software-related issues becoming a primary factor where millions of vehicles were recalled for issues ranging from rearview camera glitches to engine control logic errors.
In the SDV era, the workflow for a Field Service Action looks more like a CI/CD pipeline than a service station appointment.
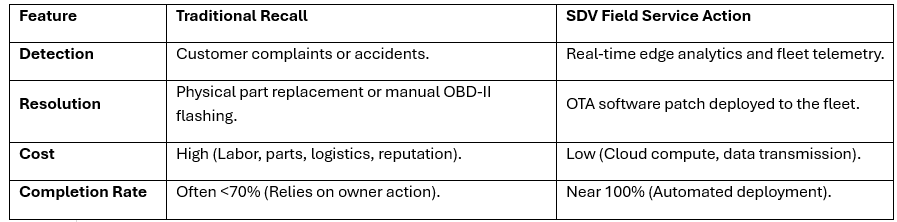
For the customer, the "recall" becomes an invisible update that happens while the car is charging in the garage. For the engineer, it's a validated pull request. For the industry, it's the end of the physical recall as we know it.
The Future: Software as a Revenue Stream
Automakers (OEMs) are transforming recalls into a new software-driven business model. Instead of bringing vehicles in for physical fixes, over-the-air (OTA) updates allow manufacturers to repair, enhance, or even upgrade cars remotely. This enables the rise of Functions-on-Demand (FoD), where customers can subscribe to added performance, advanced driver assistance features, or battery improvements.
As vehicles become software-defined (SDVs), the traditional recall is being replaced by continuous, data-driven updates that make cars safer and more capable over time. In this shift, Technical Program Managers play a key role – bridging fast-paced software development with hardware safety standards. Their focus moves from managing physical parts to guiding ongoing product evolution through automated validation, unified issue management, and resilient system design.
By integrating customer insights and BEV ecosystem data back into the design phase, we ensure that the next software-defined "recall" isn't a fix for a mistake, but a scheduled enhancement of the product’s lifecycle.
Tags: Automotive SDVs field service actions